Ethical Hacking Training In Chennai | Ceh Course In Chennai
- - Category: Online Education
- - 11 Jul, 2023
- - Views: 38
- Save
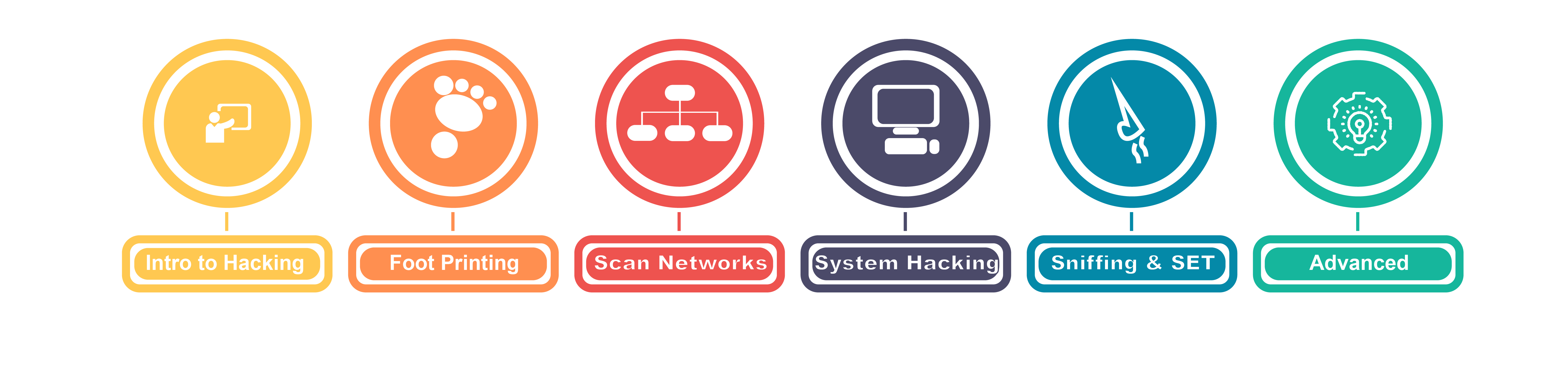
Learn CEH Training from Professional Hackers in 50+ hours. Join Ethical Hacking Training in Chennai @ Bitaacadem
Ethical Hacking Training in Chennai
Want to obtain your Ethical Hacker certification? Let’s get started. BITA Academy provides the best Ethical Hacking Training in Chennai, instructing you in the most recent hacking tools, methods, and commercial-grade hacking software used by hackers and information security experts to breach a corporation legally. It has created a brand-new framework for learning that employs a four-phase technique: Learn, Certify, Engage, and Compete. After finishing this course, you will be able to use information security controls, legislation, and standards.
What is Ethical Hacking?
A permitted attempt to acquire unauthorized access to a computer system, application, or data constitutes ethical hacking. An ethical hack entails copying the tactics and behaviors of hostile attackers. This procedure aids in locating security flaws that can subsequently be fixed before a malicious attacker can take advantage of them.
Ethical hackers, also called “white hats,” are security professionals who carry out these security evaluations. They contribute to strengthening an organization’s security posture through their proactive activities. The goal of ethical hacking is different from malicious hacking because it is done with permission from the organization or owner of the IT asset.
Roles and Responsibilities of Ethical Hacker
To hack lawfully, ethical hackers must adhere to specific duties and obligations. Ethical hackers will abide by these rules since they know their obligations. Some of the most significant ethical hacking guidelines and responsibilities are listed below:
- Before any security evaluation, an ethical hacker must request the required authorization and consent from the organization.
- They must decide the parameters of their evaluation, make a strategy, and then provide it to the organization with instructions on what to do, when to do it, and how to do it.
- Ethical hackers must report any security flaws and vulnerabilities uncovered in the system or network.
- Keep their findings a secret. Ethical hackers should consent to and abide by their non-disclosure agreement because they aim to secure the system or network.
- After scanning the system for vulnerabilities, these hackers should remove all evidence of their intrusion. By doing this, they stop other malicious hackers from exploiting the system’s vulnerabilities.https://bitaacademy.com/course/ethical-hacking-training-in-chennai/